"This plane was designed by an overpaid baboon and assembled with milk cartons and duct tape. Make sure you follow the checklist so everyone knows its safe."
If that isn't #infosec and #SoftwareEngineerimg in a nutshell, I don't know what is.
"This plane was designed by an overpaid baboon and assembled with milk cartons and duct tape. Make sure you follow the checklist so everyone knows its safe."
If that isn't #infosec and #SoftwareEngineerimg in a nutshell, I don't know what is.
I realized I hardly ever add topical hashtags to posts which probably makes it tougher for folks around the fediverse to see things I write that they might be interested in. I'll try to do better with future posts about #weaving , #calculators , #addingmachines and #Linux #FOSS and #infosec topics.
I have an awesome friend at Code for America, a non-profit based in SF (with some remote positions) that helps government better serve its people. They're working currently in safety net services, criminal justice reform, and easing the EITC participation gap.
They're also currently hiring for security engineers:
- https://www.codeforamerica.org/jobs?gh_jid=2036230
- https://www.codeforamerica.org/jobs?gh_jid=2036206
Oh, and the pay is quite nice! Apply online, or ping me if you'd like to connect with my friend. Please boost! #infosec #jobs
Hey there's *another* Steam zero day! Oh and steam banned the researcher, and continues to lock/close reports about them and making insufficient patches to "fix" them. So... that's... what it is. So many reasons to hate Steam anymore, particularly they're stranglehold on the 300+ games I "own" on there *cries* Why did I let this happen
Holy what!
"Amazon's home security company Ring has enlisted local police departments around the country to advertise its surveillance cameras in exchange for free Ring products and a “portal” that allows police to request footage from these cameras, a secret agreement obtained by Motherboard shows."
GnuPG — "SKS Keyserver Network Under Attack":
https://gist.github.com/rjhansen/67ab921ffb4084c865b3618d6955275f
"If you fetch a poisoned certificate from the keyserver network, you will break your GnuPG installation."
"High-risk users should stop using the keyserver network immediately."
~=8 Character Passwords Are Dead=~
New benchmark from the Hashcat Team shows a 2080Ti GPU passing 100 Billion password guesses per second (NTLM hash).
This means that the entire keyspace, or every possible combination of:
- Upper
- Lower
- Number
- Symbol
...of an 8 character password can be guessed in:
~2.5 hours
(8x 2080Ti GPUs against NTLM Windows hash)
Hey #InfoSec, anybody has heard/used/analyzed "FirstPoint MobileGuard"?
http://www.firstpoint-mg.com/full-mobile-guard/
They make some extraordinary claims, and I don't see any whitepapers nor tech literature available to support them. Perhaps I am missing something?
With all my gripes with# Signal (centralized, non-federated, server-based, Electron-based desktop app), the fact that in my circle of contacts it's not longer the "pretty good solution we should be using" but the "pretty good solution we are using but looking for something better" is such a win.
I just wanted to stop for a second and appreciate that.
If we're talking about the need to move to something better than Signal, we are in a pretty decent place.
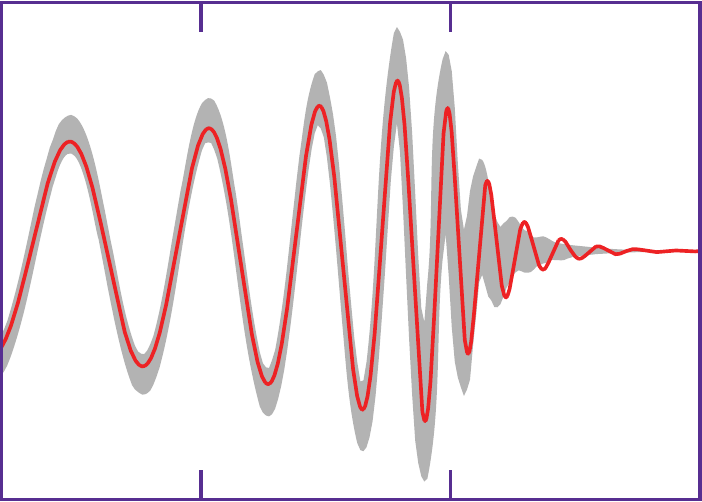
One of the paradoxes I struggle with in my work, is the conflict between crypto and reliability.
Crypto is important. But it is very binary in nature - either the stars align and you can decrypt, or it fails and there's no recovery. With that kind of binary, reliability suffers. This is inevitable.
As an example, most of the Mastodon downtime I've experienced has been related to minor SSL certificate blunders.
I feel like most of the #InfoSec community wilfully ignores this dynamic.
Oh boy. https://github.com/signalapp/Signal-Desktop/issues/1635
tl;dr Signal Desktop is based on Electron, which in turn is based on Chromium 58-59, and it seems to be affected by bugs that have been fixed in Chrome/Chromium 60-62.
Gotta love #Electron. As somebody said "now everyone is running 5 different instances of old insecure versions of the most scrutinized and attacked application on Earth."
Wait, what. Windows 10 sends info on USB devices plugged in directly to Microsoft?
And it does that using pure HTTP?
https://pastebin.com/ttYp5rLg
You gotta be kidding me.
Wow, this is old news (June 2017), but... how can I support this?
https://www.engadget.com/2017/06/19/eu-proposes-banning-encryption-backdoors/
"The European Parliament has proposed amended regulation that would not only require end-to-end encryption when available, but forbid backdoors that offer guaranteed access to law enforcement. EU residents need to know that the "confidentiality and safety" of their data is "guaranteed," according to the draft, and backdoors risk "weakening" that privacy."
"if you are publishing research behind a paywall, I don't know what you are doing, but it isn't Science."
"If you don't publish everything necessary to reproduce, including hardware decisions and settings, it isn't Science."
Not sure what is more shocking:
A CA having 23k private keys of their customer's certs and the CEO emailing them: http://blog.koehntopp.info/index.php/3075-how-not-to-run-a-ca/
A CA having a website which allows RCE as root, from a website input: https://arstechnica.com/information-technology/2018/03/trustico-website-goes-dark-after-someone-drops-critical-flaw-on-twitter/
I'm just speechless.
Flight-sim devs say hidden password-dump tool was used to fight pirates
Installer ran a "Chrome Password Dump" tool on copies suspected of piracy.
Can't find an english language news source for this, but it seems that #Microsoft Defender is flagging files that contain short strings (like "Squeamish Ossifrage" or "malicious_x = %p") from the #Spectre PoC as malware: https://m.heise.de/security/meldung/Microsoft-stuft-das-PoC-Programm-zu-Spectre-als-boesartig-ein-3959995.html
This is obviously useless for actual threat detection, so are they trying to find people who are playing with the PoC code?
#infosec
Chirp! is a social network. It runs on GNU social, version 2.0.1-beta0, available under the GNU Affero General Public License.
![]() All Chirp! content and data are available under the Creative Commons Attribution 3.0 license.
All Chirp! content and data are available under the Creative Commons Attribution 3.0 license.